Friday, March 21, 2008
This video was suggested to me by my friend Arun Kumaar.An excellent video of 26 seconds.You will definitely enjoy watching it.
Labels: Fun
Google has included invisible mode feature in GMail Chat last month(Feb 22, 2008). This feature allows you to appear offline and still chat with your friends unlike MSN Messenger. I feel that this is one of the best feature in Yahoo Messenger which is now made available to us in GMail Chat. Please note that this feature is not availble on GTalk Clients. Check out GMail’s Official Blog for more information.
Hope this invisible status is reaches gtalk soon.
Labels: GMail Tricks, GOOGLE, Gtalk
Thursday, March 20, 2008

The regular chess rules are used, although the shape of the board is obviously different.

This is an empty board. Every player has 16 standard chess pieces.

The pawn moves as usual straight forward and takes enemy pieces one square diagonally forward.
The rook moves as always. Nothing new.
The knight is also no different from a standard knight.
Nothing new for the queen as well.
One peculiar feature: the diagonal in the center of the board.

General rules:
Labels: Chess
Tuesday, March 18, 2008
Now the solution for your problem is given below.....
Step 1:Copy the Address of your desired folder from address bar for example if it is C:\FAV copy it(its location on ur hard drive)
Step 2:Goto C:\ drive,goto Tools-->Folder Option-->View-->Hidden Files and Folders-->Hide protected operating system files(Recommended)-->Unhide Hide protected operating system files(Recommended)
#It will give a warning,don't worry!!!
Step 3:Goto C:\Documents and Settings\Administrator\SendTo
#In place of Administrator its your User name
Step 4:Right Click --> New--> Shortcut.Paste The name of your desired folder in "Type the location of the Item" Text Field for Example C:\Fav -->Next-->Finish
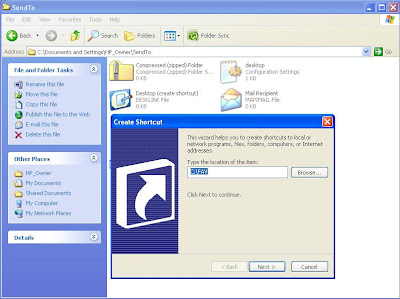
Step 5:Goto C:\ drive,goto Tools-->Folder Option-->View-->Hidden Files and Folders-->Hide protected operating system files(Recommended)-->Hide Hide protected operating system files(Recommended)
#Step 5 is optional
You may browse ur desired folder also.....
Article idea:http://www.computerlords.blogspot.com/
Labels: Windows corner...
Medical Science Report says: When the mother of this chid was pregnant, she had 2 foetuses inside her, but one of the foetus grew inside the other, this is why this girl was born with the other foetus inside her womb.


Labels: Medical Miracles, News
Sunday, March 16, 2008

Having read Dan Brown’s work of DaVinci Code I got interested in reading Digital Fortress, especially knowing that it’s background theme is computers and cryptography. In DaVinci Code, most of the facts look to me like they are accurate, perhaps because I’m not an expert in any of the fields they touch (neither art, fossils or the Vatican situation). But I know something more about computers and I have always liked cryptography, and having read the book,I wanted to know whether the things mentioned in the book is true, I found some things which don’t really fit.
Plot summary(taken from wikipedia)
Susan Fletcher, a brilliant mathematician and head of the National Security Agency's (NSA's) cryptography division, finds herself faced with an unbreakable code named "Digital Fortress", which is resistant to brute-force attacks by the NSA's 3 million processor supercomputer dubbed "TRANSLTR". The code is written by Japanese cryptographer Ensei Tankado, a fired employee of the NSA, who is displeased with the agency's intrusion into people's privacy.
Tankado auctions the algorithm on his website, threatening that his accomplice "North Dakota" will release the algorithm for free if he dies. Tankado is found dead in Seville, Spain. Fletcher, along with her fiancé, David Becker, a skilled linguist and a Professor, must find a solution to stop the spread of the code.
The plot looks really fine,but the informations in this book are not really fine.Some of these things are what we could call “artistic licenses”, where the author has invented something which doesn’t really exist so the novel is interesting, but others are factual errors which look like Dan didn’t get really documented about it. And it’s a pity, because he says two ex-NSA cryptographers contributed to the book and they should know much better what they were talking about.
WARNING: For those who haven’t read the book and have the intention of doing it, this contains all kind of spoilers.
“The notion of a rotating cleartext function was first put forth in an obscure, 1987 paper by a Hungarian mathematician, Josef Harne. Because brute-force computers broke codes by examining cleartext for identifiable word patterns, Harne proposed an encryption algorithm that, in addition to encrypting, shifted decrypted cleartext over a time variant. In theory, the perpetual mutation would ensure that the attacking computer would never locate recognisable word patterns and thus never know when it had found the proper key. The concept was somewhat like the idea of colonising Mars—fathomable on an intellectual level, but, at present, well beyond human ability.”
Although the mentioned mathematician didn’t really exist we could try to believe in the concept of rotating-cleartext but this doesn’t stand. So, an algorithm which produces data that variates over the time so you can’t know whether you got the real data or not. OK, then how does the intended receiver know the data? He will need something more (taking in consideration that this could really work), like the time when it was encrypted and the current time. These will be simply more bits in the keyspace to be brute-forced, so you can always find the original content.
Susan had learned about the Bergofsky Principle early in her career. It was a cornerstone of brute-force technology. It was also Strathmore’s inspiration for building TRANSLTR. The principle clearly stated that if a computer tried enough keys, it was mathematically guaranteed to find the right one. A code’s security was not that its pass-key was unfindable but rather that most people didn’t have the time or equipment to try.”
OK,I never knew there was one such principle, (maybe another invented name). It seems nobody has ever heard about Bergofsky Principle outside this book and for a reason(I spent lot of time in searching about it). It says “mathematically guaranteed to find the right one”, but it would be only correct if it said “mathematically guaranteed to test the right one”.
That is the concept behind brute-force: try all the possible keys, so it’s sure one of them will be the correct one. The difficult part is how to know if the one we tested was the correct one. But, let’s talk about One-time pad, an encryption algorithm “which has been proven, from theoretical first principles, to be unbreakable when properly deployed”.
It works because the key-length is the same as the length of the data, so a lot of different keys will give results which might look like plausible. From a message encrypted with this algorithm you can find the original text you want simply by variating the key used. So, when trying to decode one of this messages TRANSLTR is guaranteed to test the correct key, what is not guaranteed is to be able to know it’s the correct one.
“Susan had created, in effect, a directional beacon disguised as a piece of E-mail. She could send it to the user’s phony address, and the remailing company, performing the duty for which it had been contracted, would forward it to the user’s real address. Once there, the program would record its Internet location and send word back to the NSA. Then the program would disintegrate without a trace. From that day on, as far as the NSA was concerned, anonymous remailers were nothing more than a minor annoyance.”
There’s no way the tracer can work with the current state of e-mail. E-mail is just data, not executable, so the user is the one who has to execute it, it can’t execute itself to know where it is and even less make itself disappear. The only way something like this can work is with web bugs, attaching a link to the email which will be visited when the recipient receives the email and opens it, but it needs the cooperation of the recipient and can’t delete itself (well, maybe if there’s a bug in the e-mail software used to open it, highly doubtable) .
“She knew mutation strings were programming sequences that corrupted data in extremely complex ways. They were very common in computer viruses, particularly viruses that altered large blocks of data.”
This really doesn’t make any sense, so I’m considering it simply another artistic license. Even Dan himself doesn’t seem to know what he wants to represent with mutation strings, so even less do I.
“After we make the switch,” Strathmore added, “I don’t care how many pass-keys are floating around; the more the merrier.” He motioned for her to continue searching. “But until then, we’re playing beat-the-clock.”
So Strathmore’s intention is to replace the file with Digital Fortress code with an altered version of it with a backdoor so the NSA can read all messages encrypted with it. But, what if someone downloaded it previously? He will be able to get the original version without any backdoor, so the plan completely fails. Even more, he can get also the other version with the backdoor, so he will be able to compare both and find the backdoor in it.
“Now Susan was even more doubtful. Encryption algorithms were just mathematical formulas, recipes for scrambling text into code. Mathematicians and programmers created new algorithms every day. There were hundreds of them on the market—PGP, Diffie-Hellman, ZIP, IDEA, El Gamal. TRANSLTR broke all of their codes every day, no problem. To TRANSLTR all codes looked identical, regardless of which algorithm wrote them.”
When he says scrambling text into code I hope he’s not meaning executable code. But, what I don’t like about this paragraph is that he confuses different kinds of algorithms: public-key (El Gamal) and private-key (IDEA), with encryption systems, like PGP which uses the other two in combination to work. PGP is not an algorithm and neither is ZIP, this is a compression system, which can, optionally, encrypt the data, originally with a propietary protocol and nowadays using AES, an standard for encryption. (I searched for these stuffs in wikipedia and google).
““I don’t understand,” she argued. “We’re not talking about reverse-engineering some complex function, we’re talking brute force. PGP, Lucifer, DSA—it doesn’t matter. The algorithm generates a key it thinks is secure, and TRANSLTR keeps guessing until it finds it.””
Susan says the TRANSLTR can find the key even if it doesn’t know what algorithm was used. This is impossible, as you need the algorithm to test whether the key works or not. “Four-bit alpha groupings,” she puzzled. “They’re definitely not part of the programming.”
PFEE SESN RETM MFHA IRWE OOIG MEEN NRMAENET SHAS DCNS IIAA IEER BRNK FBLE LODI
Sorry, Dan, but a bit is either 0 or 1, so these are not four-bit alpha groupings. These are simply 4-character groups, where each character (if using standard codification) uses 8 bits.
“Primes were the fundamental building blocks of all encryption algorithms”
Sorry, but no. There are a lot of encryption algorithms which don’t use prime numbers as its basis, and to put it easy I’ll repeat myself in the example: “one-time pad”.
“Public-key encryption was a concept as simple as it was brilliant. […] The only way to unscramble the message was to enter the sender’s “pass-key”—a secret series of characters that functioned much like a PIN number at an automatic teller.”
Sorry, but again: NO!. this is not how public-key encryption works. If it was better explained it would be how private-key encryption works. But Dan, you need to read the Wikipedia and not say this kind of things.
“With a few quick keystrokes, she pulled up a program called ScreenLock. It was a privacy utility. Every terminal in Node 3 was equipped with it. Because the terminals stayed on around the clock, ScreenLock enabled cryptographers to leave their stations and know that nobody would tamper with their files. Susan entered her five-character privacy code, and her screen went black. It would remain that way until she returned and typed the proper sequence.”
Five character passwords in a computer managed by a NSA member? Not long enough to be credible. The most paranoid of my friends use twenty characters passwords, so I imagine NSA should use something a bit longer than 5 chars. (I myself use 10 character passwords mostly...)
Oh, and Greg manages to install a keylogger in all these computers, so I should say the system operator is not very efficient in keeping the systems secure. At least, lock the computer case inside a box so nobody can access it directly.
To finish this list, how did they plan to decipher the Digital Fortress code if they didn’t have the decryption code? OK, you get the passkey but you need the decryption code, which is encrypted with itself. Mmmm, a no-no…
Let’s get with the errors not related to computers.
In one chapter the assassin Hulohot transmits the message "SUBJECT: P. CLOUCHARDE - TERMINATED", but in another chapter the list of messages reads "SUBJECT: PIERRE CLOUCHARDE - TERMINATED". I am not sure whether this error appears in other editions of the book.(It appeared in my edition).In wikipedia it is said that the information about Seville,Spain were wrong.(I am not too sure about it)
Inspite of all this, I should say I did enjoy reading this wonderful book as much as the DavinCi Code from Dan Brown. His success lies in his art of mixing truth with fiction and making you believe that the fiction was true.If you are not an expert in cryptography then this book is definitely worth a read.
Labels: Book Review














